Alphaverse

Sometimes alpha is in protecting your wealth. The biggest issue of blockchains is the same as their most significant advantage: immutability. One wrong action can be very costly, so you need helpers to protect yourself from scammers.
You might think you’re safe, and maybe you are. But even seasoned degens like Kevin Rose can fall for dumb stuff in the heat of the moment, and losses can be devastating.
I learned it today the hard way. I jumped on my computer before having a coffee, apparently not fully awake, and clicked on some scam link. When I realized I was in a danger zone, my NFTs were already gone. Among them were Checks VV, with a current floor of 2.5 ETH.
I hope my story makes you think about your safety and that you will read this letter to the end. If you’re only interested in protection software, skip until the “Helpers” section.
EVM vs. Others
The first thing to think about is the chain you’re using. If it’s something EVM compatible that MetaMask supports, that should generally be safer than others.
The key reason EVM chains are relatively safe is that there’s a vast history of known vulnerabilities. Ironically, others have already lost money, so you don’t have to. There are safety measures in place, like token approvals.
MetaMask, in particular, is good because the team treats safety seriously. For example, there’s a mechanism to protect unauthorized code from entering the MetaMask codebase. It’s complicated tech, highlighting the team’s focus on securing users.
Non-EVM chains like Cosmos and Solana don’t have as long a history. Thus, various vulnerabilities can emerge. I once lost $4,000 on Solana, and I still don’t fully understand how that happened, even after checking the chain.
Overall, if you’re on EVM, you’re safer than on other networks, especially the new ones. Thus, going the extra mile when dealing with your funds’ security on non-EVM chains is better. I will explain how to do so in the next sections.
Transactions vs. Signatures
Transactions aren’t trivial, which is a good thing. They cost money, especially on Ethereum, so you tend to be more focused when submitting them. Plus, you primarily interact with a handful of tried and tested projects.
Stick with well-known applications like OpenSea and Uniswap. I recommend using Twitter to find them first and verify that the people you follow also follow the same account. That’s one of the most straightforward ways to avoid phishing websites.
Over 80 accounts I know follow this page, so the link is most likely safe.
If you’re going to mint an NFT or interact with a smart contract, it’s better to use a hot wallet (discussed below). Alternatively, you can watch this video: it should help you figure out what a contract will do if you transact with it. Most of you are better off with the first option.
Signatures are very dangerous. They don’t cost money but ironically can be very costly.
Don’t approve anything in your wallet until you read the information in the pop-up window. You will often see something human-readable, and this type of message is relatively safe. Stop if you see some gibberish like a “0x…” string or a bunch of 1s and 0s.
The problem is that you aren’t 100% focused all the time, so you can accidentally miss a malicious signature. There’s no indication of potential danger, which might confuse you. Thus, a hot wallet (discussed below) is handy.
Hot, Warm, and Cold Wallets
Having several wallets is tedious, but organizing yourself like this is better than having most of your money vanish.
Cold wallets, or vaults, are for storage only. Here’s what distinguishes them:
- Private keys are stored securely. Every crypto wallet has a private key (words you get when creating the wallet). When creating cold wallets, you should be extra careful with how you store them. I suggest using the following solutions for storage: 1, 2, 3, 4, 5, 6, 7.
- Exist on a dedicated device. You can use Ledger, Trezor, a phone with AirGap (shouldn’t be your primary phone), a computer with MetaMask, or any other wallet (shouldn’t be your primary computer).
- Airgapped or protected from private key leakage otherwise. The wallet’s private key shouldn’t touch the digital world and the Internet much. Ledger and Trezor don’t expose your private key, while a dedicated computer or phone should be mostly disconnected from the Internet.
- Used only for direct transfers. You don’t use these wallets for trading or anything else. No apps, only simple transfers.
- Persistent. You usually don’t change these wallets.
- Store 99+ percent of your wealth.
- (Optional) Multi-sig. You can have several addresses controlling a vault, and Safe is one of the best tools for it. If one of your addresses is compromised, others will act as a shield against withdrawal.
- (Optional) Password protected. Few know, but hardware wallets like Ledger and Trezor can have passwords that completely change addresses available to access. Ledger users can learn how to set them here. Trezor has them in the user’s interface.
Hot wallets are the complete opposite.
- Private keys are stored on paper. You shouldn’t store your private keys digitally, but buying specific hardware for hot wallets is overkill. Use a notebook that you keep somewhere safe.
- Easily accessible. You should have this wallet in your browser, ready to open and do anything anytime.
- Used for all kinds of transactions. You can go full degen mode if you keep the next rule in check.
- Store less than 1 percent of your wealth. You don’t want to lose more than 1% due to not being focused enough.
- Rotated. Rotating hot wallets is healthy and will protect you from potential vulnerabilities that might have weeks or months between your address being exposed and the exploit happening.
Warm wallets are somewhere in the middle. They are required when you need to operate with over one percent of your total worth. Having a warm wallet requires some helpers.
Helpers
Helpers will help you protect yourself from accidents. They will either restrict who can move funds or display warnings before you have to do something.
Harpie and Wallet Guard
Harpie and Wallet Guard are security suites. Wallet Guard can be used for any type of wallet. It checks the websites you visit and the extensions you have. If something is wrong, it alerts you, and you can address alerts in the app’s dashboard.
Harpie fits cold and warm wallets more but can be used for any wallet. It establishes a trusted network to which you can easily add all popular DeFi and NFT apps of addresses. When your asset is moved outside of the network, the transaction fails, and your asset ends up in Harpie’s vault. You can recover your assets from there to an uncompromised address anytime you want.
Delegate.cash
Delegate.cash lets you prove ownership of high-value items you store on your cold wallets while using a hot wallet. It may come in handy to gain access to token-gated discords or other websites. Setting everything up is simple: connect your cold wallet and link with your hot wallet by clicking a button.
The website can also let your cold wallet transfer NFTs through a warm wallet. It has an “NFT” tab that allows you to approve rights for a single NFT right before using it from a warm wallet. Remember: cold wallets DON’T touch applications.
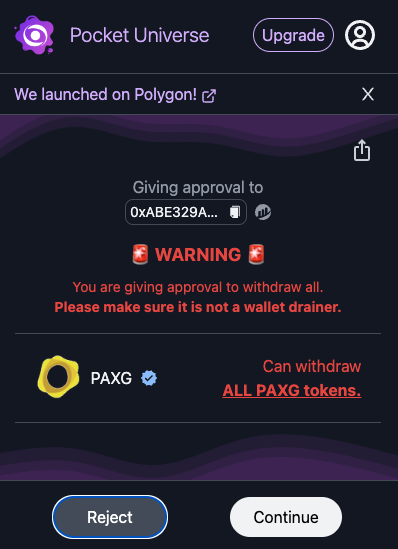
Stelo and Pocket Universe
Stelo and Pocket Universe are for your hot and warm wallets. They will decipher signatures and simulate transactions before your MetaMask window pops up. If something is wrong, you will see a warning before you can do anything.
There’s also a Fire extension, but it doesn’t block your MetaMask, so you might still make mistakes in the heat of the moment. Don’t use it.
As you can see, the helpers I mentioned are for EVM because that’s what we usually use. However, you can find alternatives on other networks. For instance, here’s a multi-sig on Aptos.
All the helpers will work better together and in combination with wallet separation, and you being overall organized and focused. Any system is as secure as its weakest link, and we are the weakest link most of the time. I hope this email will help you with ensuring personal security on-chain.
Stay safe.